
Well, the truth is - according to bookkeeping and accounting - it can be a capital expense or, in many cases, that’s an operating expense. However, that’s far from the big picture.
Business Process Outsourcing of Software Development and Related Services can bring the following benefits:
- Save a fortune on inventing and building an own product, service or infrastructure from the scratch
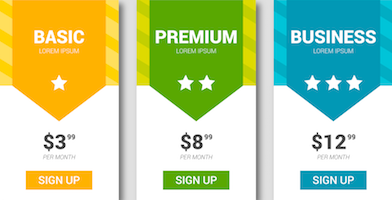
- Leverage of ready infrastructure and service “here and now” for a very reasonable pricing
- Avoid wasting money on high-level expectations
- "Fixed Price" for an Expected Revenue
So, let’s check the bigger picture using the most common cases.
#1 A Subscription Model
As a business manager or head of a specific department of the corporation, you perhaps using one or more subscriptions or business process outsourcing services. It might be cloud services you are renting, online ads, pay per click, telecommunication services or even delegating Customer Support Level 1, Level 2, Level 3 to your vendors.
It is a normal, a usual service for the definitely fair pricing. Indeed, it’s cheaper to delegate this to the vendor than to build the whole infrastructure, which will cost you a fortune, moreover your business or corporation is targeting a very another market and IT services are far from the primary focus. So, the subscription model is very cost efficient and saving a small fortune for you and your corporation every month, every quarter, every year.
It removes from your sight all problems and mechanic of the service making possible to build your own business on top of it. Huge retail corporations are building their online stores, increasing efficiency of their logistics departments, multiplying their annual sales and all this for a very reasonable price, thousand times less comparing it to the investments they have to make doing it as a part of their business, here and almost now - for sure it’s faster to take something existing and already operating in a business as usual mode. By the way, Business As Usual (BAU) is a yet another long story related to established and constantly tuned business processes inside this “black box” of business process outsourcing resulting a very complex and specific Service Level Agreement (SLA) for the customers.
All above made a possibility of the creation of a couple more types of Subscriptions models:
- Transaction-Based Model - customer pays per actual transaction
- Managed Service - customer pays for specific SLA
For instance, Am-Pro provides Managed Service of cloud support and maintenance (W33 package). Let’s conclude this section.
Subscription model - is a sort of business process outsourcing, based on a reasonable price. It can give your business or corporation a leverage of ready infrastructure and service “here and now” for a very reasonable pricing.
#2 A Fixed Price / Cost Plus Model

That’s a typical project model when a customer really knows in details what’s required. A “Fixed Price” for a set list of requirements. Indeed, it was good 20 years ago, therefore any uncertainty in requirements leads to the “Cost Plus” model, which anticipates a certain, specific percent of a contingency budget for everything unexpected. So, by the end of the day, there is a complete product or functional module ready for a “Fixed Price/Cost Plus” capital expense made. Indeed, the “Fixed Price” doesn’t mean “Fixed Risks”. the final product can be of a very different quality: a Proof of Concept, a Minimal Viable Product or a Product/Functionality Ready for the Market or an Internal Client. For sure, basing on our experience the final product requires some back-n-force iterations to make it apt and ready. Nevertheless, that’s normally expected in our quotes.
So, what’s is a benefit for a business by the end of the day? It depends. For instance, if there is a great visionary, (imagine Steve Jobs) there is a real roadmap from an expense to a revenue and a profit. if the business has no visionary - we can help with our vision and potential benefits. For instance, let’s imagine that a telecom company wants to put their products and services on Blockchain rails. There are several potential futures:
- the market will resist. regulations will make a product roadmap very complicated. Finally, the return on this investment will be doubtful.
- there are anticipations, like that blockchain, by its nature, will eliminate almost all frauds, which aren’t supported by real algorithms and processes. By the end of the day, pink dreams will dissolve in a hard as a rock reality, that vast majority of frauds is not related to the field which was “Blockchained”.
- there are a clear vision and understanding, based on a real experience of implementation. The conservative numbers of how it can positively impact the business. For instance, the same Blockchain and the well-known “Blockchain for a Supply Chain” architecture can be used. All benefits are well-known and can be easily calculated. As result, a business will receive a very apt tool, save some operating costs, and receive a certain competitive advantage on the market.
Conclusion:
The Fixed Price / Cost Plus Model requires a clear understanding of the benefits. A Requestor must have a visionary or use an expert visionary. This way it’s easy to place the correct expectations and calculate a final ROI of any project, therefore it will be a "Fixed Price" for an expected Revenue.
By the way, after the project is done the subscription model, related to technical support, cloud and other related services can be applied.
The next article about BPO is here >>